10 Essential Steps to Identify OT Security Risks and Action Plan to Mitigate Gaps
- FutureSpex

- Mar 30
- 3 min read
Operational Technology (OT) systems are the backbone of manufacturing companies, controlling critical processes and machinery. Yet, these systems often face growing security risks that can disrupt production, cause financial losses, or even threaten safety. Identifying OT security risks early is crucial to protect your operations and maintain business continuity. This blog post outlines 10 essential steps to check your OT security risks and provides a clear action plan for each step if gaps are found. By following these steps, manufacturing companies can build awareness of OT security challenges and understand the value of investing in OT security competence through professional training.
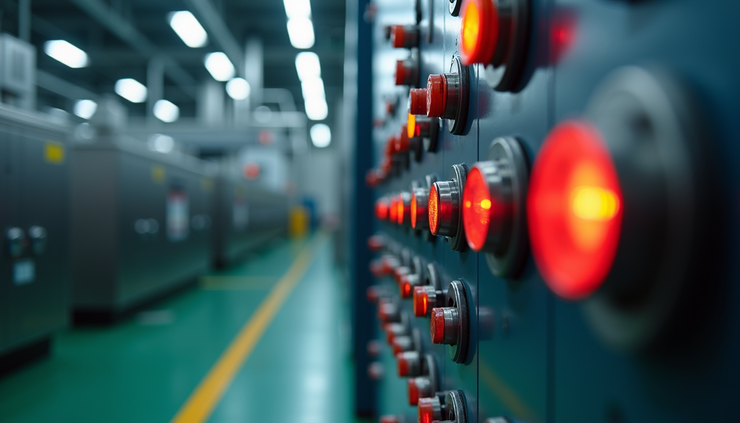
Industrial control panel with warning lights and switches representing OT security environment
1. Map Your OT Assets and Network
Start by creating a detailed inventory of all OT assets, including controllers, sensors, actuators, and network devices. Understand how these assets connect and communicate within your network.
Action plan if not checked:
If you lack a comprehensive asset map, prioritize conducting a thorough OT asset discovery using automated tools or manual audits. This map forms the foundation for all security efforts.
2. Assess Network Segmentation
Evaluate whether your OT network is properly segmented from IT and external networks. Segmentation limits the spread of cyber threats and isolates critical systems.
Action plan if not checked:
Implement network segmentation by creating zones and conduits based on risk levels. Use firewalls and access controls to enforce boundaries between OT and IT environments.
3. Review Access Controls and User Permissions
Check who has access to OT systems and whether permissions follow the principle of least privilege. Unauthorized or excessive access increases risk.
Action plan if not checked:
Establish strict access control policies. Use role-based access control (RBAC) and multi-factor authentication (MFA) to secure user accounts and limit access.
4. Evaluate Patch Management Practices
Determine how often OT devices and software receive security updates. Many OT systems run legacy software that may lack regular patches.
Action plan if not checked:
Develop a patch management schedule tailored for OT, balancing security needs with operational stability. Test patches in controlled environments before deployment.
5. Analyze Incident Detection and Response Capabilities
Check if your organization has tools and processes to detect OT security incidents quickly and respond effectively.
Action plan if not checked:
Invest in OT-specific monitoring solutions and train staff on incident response procedures. Establish clear communication channels for reporting and managing incidents.
6. Verify Backup and Recovery Procedures
Ensure that critical OT system configurations and data are regularly backed up and can be restored promptly after an incident.
Action plan if not checked:
Implement automated backup routines and test recovery processes regularly. Store backups securely, preferably offline or in isolated environments.
7. Examine Physical Security Controls
Physical access to OT equipment can lead to tampering or sabotage. Review how well physical security measures protect your OT assets.
Action plan if not checked:
Enhance physical security with locks, surveillance cameras, and restricted access areas. Train personnel to recognize and report suspicious activity.
8. Check Compliance with Relevant Regulations and Standards
Identify which industry regulations and standards apply to your OT environment, such as IEC 62443 or NIST guidelines, and assess your compliance status.
Action plan if not checked:
Conduct a compliance audit and develop a roadmap to meet regulatory requirements. Use standards as a framework to improve your security posture.
9. Evaluate Employee Awareness and Training
Human error is a common cause of security breaches. Assess whether your staff understands OT security risks and follows best practices.
Action plan if not checked:
Enroll employees in specialized OT security training programs. Our OT Security Professional course fast-tracks employee knowledge on regulations, standards, and risk management.
10. Review Third-Party and Vendor Security
Third-party vendors often have access to OT systems. Evaluate their security practices and the risks they introduce.
Action plan if not checked:
Implement strict vendor management policies, including security assessments and contractual requirements. Limit vendor access and monitor their activities.
Building strong OT security requires ongoing effort and expertise. These 10 steps provide a clear path to identify risks and close gaps in your manufacturing environment. Investing in employee training, such as our OT Security Professional course, equips your team with the skills to manage risks effectively and comply with evolving standards.
Taking action now helps protect your operations from costly disruptions and builds a culture of security awareness. Start your OT security journey today by assessing your current state and planning targeted improvements.




Comments